

Web23 and Cyberscope Audit - Case Study

Web23 - Smart Domains Tokenized on Hedera
Web23 is a DNS platform. It allows users to register and tokenize domain names based on Hedera Hashgraph. It aims to provide utility and accessibility to the domain industry. Web23 focuses both on Web2 and Web3 technologies. They have implemented a service on the blockchain that allows users to buy, sell and manage their domain names.
Hedera Hashgraph is a distributed ledger technology (DLT) platform that uses a novel consensus mechanism called "hashgraph consensus" to achieve high levels of performance, security, and decentralization.
The Web23 mission is to dominate both Internet Corporation for Assigned Names (ICANN) Web2 and Web3 domain name registration. They are moving forward to fill the gap between Web2 and Web3 by integrating the decentralized world into the browser. This will essentially bridge the Domain Name Service (DNS) to the DLTs technology.
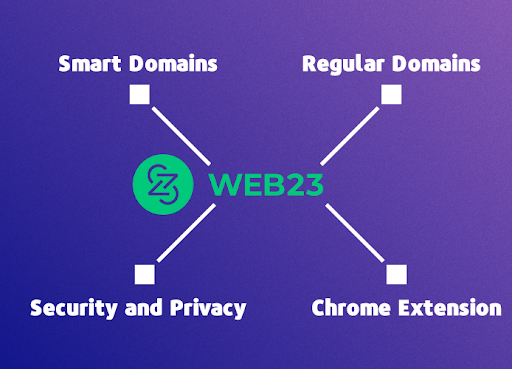
The Web23 ecosystem consists of many sections, including the Smart domains, Regular domains, security, and tools like the dashboard and the Chrome extension.
Smart Domains
The users have the ability to search and purchase domain names. The purchase process is implemented by minting NFTs as domain name collateral. Users can assign the Smart Domains to Smart functions via a powerful dashboard.
Regular Domains
Web23 provides functionality for regular domains as well. The corresponding smart domain features are also available in the Web2 domains. The users can purchase ICANN domains. Additionally, they can transfer and manage their holdings from the Web23 dashboard. Both Web2 and Web3 administration is achieved from the same platform.
Security and Privacy
The Web23 ecosystem has implemented an algorithm that scans for potential look-alike domains. This algorithm protects the user’s identity and prevents phishing attacks.
Chrome Extension
Web23 has also developed a Google Chrome extension to provide access to Smart Domains. The extension turns the .hbar extension into a meaningful token. When a Smart domain address is typed in the Chrome extension, the DNS is resolved and it accesses the decentralized data.
Requirements
Web23 has a challenging infrastructure that consists of many entities like the Dashboard, the Chrome Extension, and the Web3 service. The main focus of the Web23 team was to ensure that the Web3 part is robust. They were aiming to make clear that their functionality does not produce any vulnerabilities. Their main requirement consists of a powerful audit assessment that will investigate all the aspects of their web3 section. Additionally, they were searching for a full-coverage thorough testing report that will cover all the potential scenarios. The Cyberscope team discussed with the Web23 team all their requirements and then they created a thorough plan for the two parts of the assessment delivery process.
Unit Tests
Unit tests in the context of a blockchain project are tests that are used to verify the functionality of individual units of code in a Solidity smart contract. The purpose of unit tests is to ensure that the individual units of code in a smart contract are working correctly. This can help to identify bugs and other issues in the early stages before the production release. A well-formed exhaustive unit test implementation could save time and resources in the long run.
The Web23 team provided a document with all the sections that the unit tests should cover. The Cyberscope team’s mission was to enrich these scenarios with as many cases as possible. They had to identify all the aspects of the application to create meaningful testing scenarios. These scenarios should provide 100% code coverage and business logic validation both in the normal and the edge cases.
The Cyberscope engineers defined a set of test cases that exercise various scenarios and inputs for the contract. These test cases are then run against the contract code to verify that it is functioning correctly.
Hardhat was the tool that was chosen as the testing framework. Hardhat contains built-in support for unit tests. It is a convenient tool for developing and testing Solidity code. It also provides a simple and intuitive way to write and run tests for smart contracts.
As an integral part of the auditing process, 15 scenarios were scripted to test the contract’s functionality. The numbers in parenthesis are depicting the corresponding Web23 document scenario. The bullets without parenthesis are additional scenarios that the Cyberscope team created.
- Should receive payment and mint successfully (1,6)
- Should setDomainAsset successfully (1,2)
- Should return empty value in an unregistered domain (1)
- Should check if the domain exists
- Should check if the sender is the owner
- Should blacklist a domain (3)
- Should not allow an unregistered domain
- Should allow a registered domain (4,7)
- Should update the site address (5,7)
- Should update the site address only from the owner (5)
- Should not allow changing an unregistered site address (5)
- Should book a domain when payment received (6)
- Should get all registered domains (8)
- Should check that domain exists (9)
- Should receive multiple payments (7,9,10)
The unit tests are included in the delivery folder in the Cyberscope audit repository. Read the unit tests here.
Audit Assessments
The Web23 ecosystem mainly consists of two entities. The Hedera integration and the Smart domain registry. So the audit should take into consideration these two entities and the combinations between them. The team should investigate a variety of cases. For example:
- A user can exploit the contract and take access to an unauthorized domain.
- A user can purchase a domain without paying fees.
- Users can pass unexpected values to the registry.
The Cyberscope team always uses more than one auditor in order to create a comprehensive audit report. The auditors collaborate with each other and combine their findings if there are any differentiations. Their initial task was to get a comprehensive understanding of the Web23 ecosystem. They thoroughly went through the documentation, the required business logic and the Hedera API integration. Then, they proceeded to do a manual line-by-line check audit of each smart contract. At this point, the Cyberscope auditors pointed out to the Web23 team some medium and high criticality findings.
Severity | Code | Title |
| Critical | BFA | Booking Functionality Abuse |
| Medium | BLC | Business Logic Concern |
| Medium | RVC | Return Value Conflict |
| Minor/Informative | CO | Code Optimization |
| Minor/Informative | CR | Code Repetition |
| Minor/Informative | RIC | Range Index Check |
| Minor/Informative | DSC | Domain Sanity Check |
| Minor/Informative | ASC | Address Sanity Check |
| Minor/Informative | RSV | Redundant State Variable |
| Minor/Informative | PAE | Precondition Abort Explanation |
| Minor/Informative | USV | Unaccessible State Variable |
| Minor/Informative | MMN | Μisleading Method Name |
| Minor/Informative | L01 | Public Function could be Declared External |
| Minor/Informative | L02 | State Variables could be Declared Constant |
| Minor/Informative | L04 | Conformance to Solidity Naming Conventions |
| Minor/Informative | L05 | Unused State Variable |
| Minor/Informative | L09 | Dead Code Elimination |
| Minor/Informative | L11 | Unnecessary Boolean equality |
| Minor/Informative | L14 | Uninitialized Variables in Local Scope |
Critical Severity Finding
Any user could exploit a method limitation and purchase smart domains with zero price, without limit. This vulnerability could be manipulated by the attacker and produce unwanted issues. The Cyberscope team brought up the finding with the developers of the Web23 team. Since it was not just a code glitch, but a business logic decision, they suggested ways that it could be addressed in order to avoid being exploited in the future.
Medium Severity Finding
The smart contract implemented an algorithm to determine the location of the dot (.) delimiter. This algorithm wrongly assumed that there was no delimiter even if the delimiter was the first character of the domain.
Read all of the findings on the initial delivery report here.
Feedback and Iterations
The Cyberscope team delivered a comprehensive audit report with suggestions for every finding. Sometimes the suggestions should take into consideration the expected business logic requirements. In these cases, the Cyberscope team discusses with the client about the potential approaches that they could take. Web23 developers had open communication with the Cyberscope auditors in order to clean up and address all the issues. As part of the iteration process, the teams set up further video calls in order to ensure all findings were addressed properly.
When the discussion finished, the Web23 team changed the source code with various additions and modifications. In their latest commit, they decreased the findings from 15 in the initial report to only 3 in the latest report. The most important critical and medium-severity issues were addressed.
Read the full report here.
Web23 and Cyberscope
The collaboration between Web23 and Cyberscope was essential for both parties. The cyberscope team identified various issues that could potentially create unexpected behaviour and unpredictable side effects to the Web23 ecosystem. Web23 team acted quickly to remediate all the issues reported by the auditors. After a few meaningful discussions, they created a revision of the smart contracts that addressed almost all of the issues.
Finally, the validation of the expected functionality did not stop in the audit assessment report. The Cyberscope team also delivered a full coverage unit-tests report in order to make sure that the codebase is following the expected behaviour.
Long-Term Collaboration
The Cyberscope team always goes above and beyond regarding the client’s requirements, delivery times, and expectations. Web23 and Cyberscope achieved a lot in a just short period of time by helping them secure their smart contract and allowing them to scale safely.
Web23 is a project that is growing rapidly and building tools in a variety of domains. Since the beginning of their collaboration with Cyberscope, they have implemented a Chrome extension, an administration dashboard and many more features are under development.
Cyberscope and Web23 will continue working together in order to secure their ecosystem and make web3.0 a safer place for the domain name space.

.png%3Falt%3Dmedia&w=640&q=75)

